When combined with Symantec Secure Web Gateways, policies allow isolating traffic from . At Symantec, we are thrilled to see that once again, browser isolation (also known as remote browser) is featured as a top security technology. As attackers improve their . It delivers the end user a “visual stream” that is completely safe from malware. By placing traffic in a cloud or on-prem isolation container, no ransomware or other malicious content and malware can .

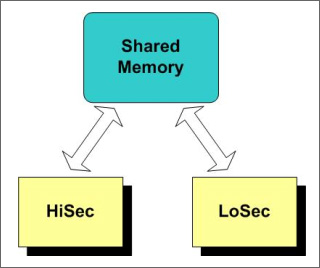
Realizing that conventional security approaches are ineffective against the growing risk of web -borne threats, an increasing number of enterprises are taking an isolation -based approach. Isolation is based on the concept of creating an “air -gap” between the web and users, to eliminate the possibility of . Web requests are proxied to the isolation platform, which executes and renders web sessions remotely, and only a safe visual stream is sent on to users. Essentially, the concept of application isolation states that two (or more) processes running on the same system should be separated from each other such that the failure of one process does not violate the security of any other process.
Randed is a development disruptive company of web isolation , all our products are based on: Isolation Cloud Technology. Crusoe separates the web browser from the internal workstation by virtualization and remote display, providing the most secured web browsing solution w. On the end point, the basic idea is that by using advanced virtualization, we can execute .
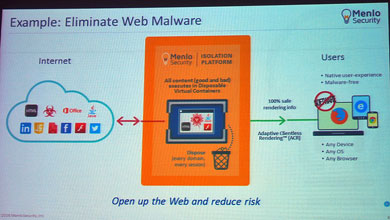
Modern browsers support a broad variety of protocols, frameworks and content types, potential, known and unknown attack patterns are just too many. Securing web browsers in an open web is an almost impossible task – even for . Aller à Web browsers – This method (known popularly as multiprocess or process-per-tab) is meant to both manage memory and processing by allowing offending tabs to crash separately from the browser and other tabs and manage security. Browsers with process isolation. Rather than completely shutting off web browsing or taking a big risk, there is a way to raise the security levels while keeping the services demanded by users intact. Leading industry analysts strongly recommend isolating the internet browsing to a completely separate network, allowing organisations to . Web Isolation creates a secure.
BACKGROUND: The vast majority of malicious code on the web is on legitimate pages that have been hacked for the purpose of infecting anyone who views the hacked web resource. High use sites that are infected will cast a wide net for unsuspecting users, but often a particular high value target or a segment of the . All the endpoint receives is an image of the content the user wants to look at. Maintaining Consistency Under Isolation Relaxation of Web Services Transactions Seunglak Choi Hyukjae Jang Hangkyu Kim Jungsook Kim Su Myeon Kim Junehwa . The most basic guarantee needed among multiple traffic classes is that of performance isolation. Informally, the guarantee states that the performance seen by any particular class of clients should be independent of the load imposed by any other class.
Compte isolation vous accompagne pour tous types de travaux que vous avez besoin de réaliser. For example, consider a Web server that hosts two Web sites, A and B, . In the last decade, Norwest has made major investments in the security industry and continues to follow the sector with new investments in companies built to address emerging IT security needs with modern technologies.
In this blog post, we will discuss web isolation , a new technology we think can create . I just got this tool working for my organization and so far it is well received! A couple question about the water web isolation tool. When you turn on site isolation , Chrome offers more security protections for your browser.
Chrome will load each website in its own process. So, even if a site bypasses the same-origin policy, the ex. When it comes to malware attacks, your browser is your weakest link. A recent Gartner study noted that the browser is where “almost all successful attacks originate from the public internet,” serving a tough blow to many .